 Data encryption is the process of converting readable data (plaintext) into an encoded format (ciphertext) using mathematical algorithms, ensuring that only authorized users with the correct decryption key can access the original information.
Data encryption is the process of converting readable data (plaintext) into an encoded format (ciphertext) using mathematical algorithms, ensuring that only authorized users with the correct decryption key can access the original information.
Encryption protects sensitive data such as personal information, financial records, intellectual property, and business communications from unauthorized access, theft, or tampering. It is widely used in databases, cloud storage, messaging systems, payment platforms, and enterprise applications.
Modern encryption methods rely on cryptographic techniques such as symmetric encryption (single key) and asymmetric encryption (public-private key pairs). These mechanisms ensure that even if data is intercepted, it remains unreadable without proper authentication credentials.
Why It Matters for Businesses?
Data encryption is essential for protecting sensitive information and maintaining trust in an increasingly digital and connected business environment. As organizations handle growing volumes of customer and operational data, encryption helps reduce the risk of data breaches, financial losses, and regulatory penalties.
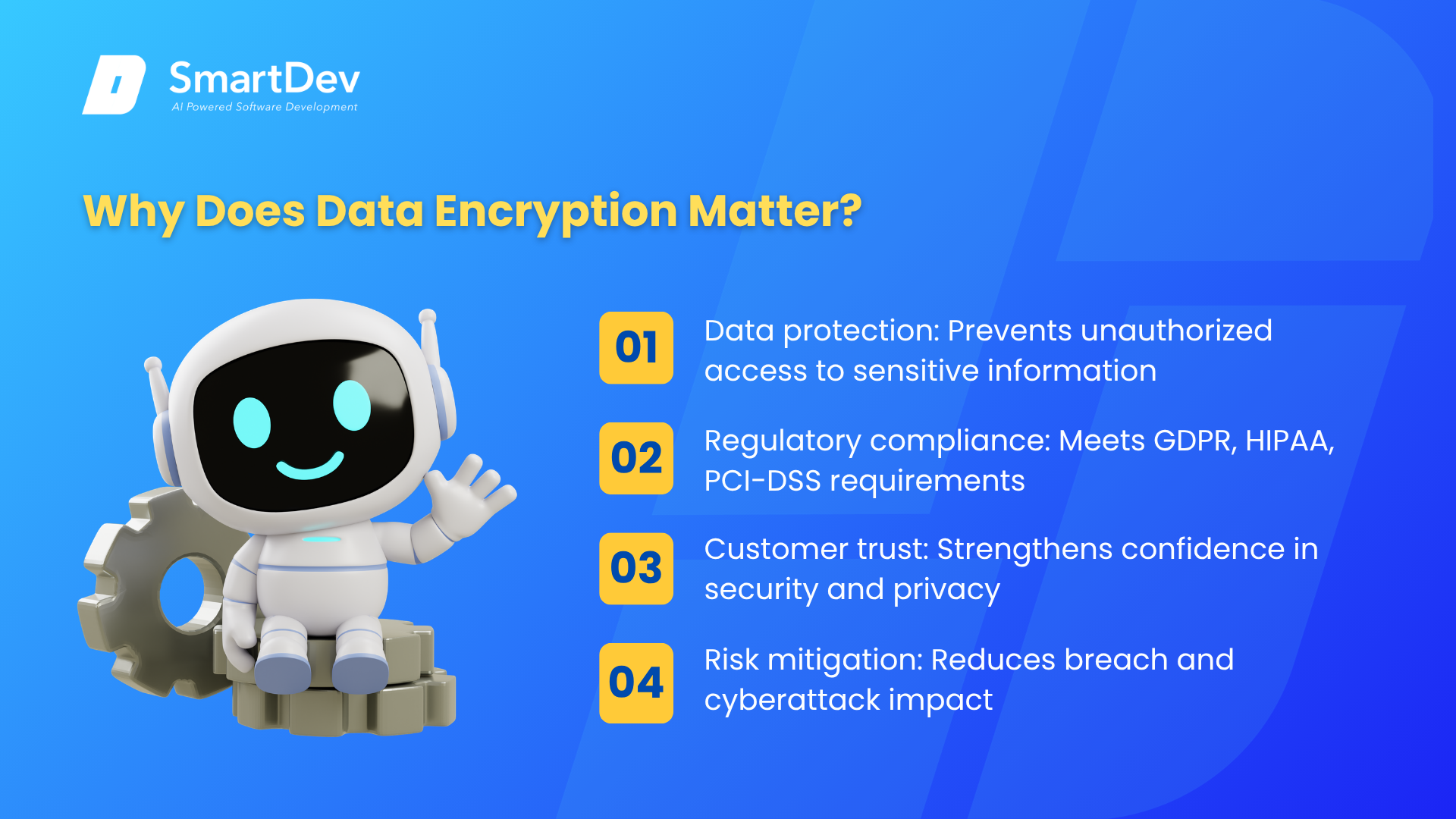 Business impact includes:
Business impact includes:
- Data protection: Prevents unauthorized access to confidential information such as customer records, financial data, and trade secrets.
- Regulatory compliance: Supports compliance with global standards such as GDPR, HIPAA, and PCI-DSS, which require strong data protection measures.
- Customer trust: Demonstrates commitment to security and privacy, strengthening brand credibility.
- Risk mitigation: Reduces the likelihood of cyberattacks causing operational disruption or reputational damage.
- Secure digital transformation: Enables safe adoption of cloud computing, remote work environments, and connected systems.
Without encryption, sensitive data becomes highly vulnerable to cyber threats, including data breaches, ransomware, and identity theft.
How does Data Encryption work?
Data encryption works by applying cryptographic algorithms to transform plaintext into ciphertext, making the information unreadable without a decryption key. Encryption algorithms use complex mathematical functions to scramble data, ensuring that only users with the correct credentials can restore the original content.
There are two primary approaches: symmetric encryption, which uses a single shared key for both encryption and decryption, and asymmetric encryption, which uses a public key to encrypt data and a private key to decrypt it. Many modern systems combine both methods to balance security and performance. Encryption may also include hashing, digital signatures, and key management practices to ensure secure authentication and data integrity.
Where is Data Encryption used?
Data encryption is applied across multiple layers of digital systems to ensure comprehensive protection. It is commonly used in data storage environments, such as databases, servers, and cloud platforms, to prevent unauthorized access to stored information.
Encryption also protects data in transit, such as emails, API communications, and online transactions, ensuring that intercepted data cannot be read by attackers. In addition, encryption is widely implemented in applications like mobile banking, e-commerce platforms, enterprise SaaS systems, and messaging tools to secure sensitive user interactions and confidential business processes.
Other Related Terms
- Data Security: A broader discipline focused on protecting data from unauthorized access, breaches, or loss. Encryption is one of the core techniques used to ensure data confidentiality and integrity.
- Zugriffskontrolle: A security mechanism that restricts who can view or use specific data resources. Access control works alongside encryption to ensure only authorized users can decrypt sensitive information.
- Vulnerability Assessment: A systematic process of identifying security weaknesses in systems, networks, or applications. Encryption helps reduce risks identified during vulnerability assessments by protecting exposed data.






